Because it’s important to know when adversaries are scanning the network searching for vulnerabilities, misconfigurations, unpatched systems or default passwords; but it’s more important to know when adversaries have already compromised a system. Aggregating this data into a unified cloud-based AI-native XDR platform like CrowdStrike Falcon may seem like an impossible task, so here is a step-by-step guide to help you avoid common pitfalls and succeed at feeding any events into it, with examples tailored specifically for SQL Server.
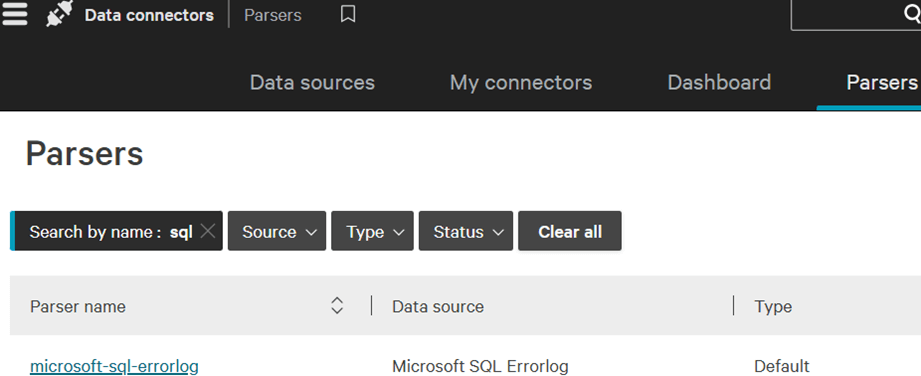
Pitfall # 1: the parser
This is the piece responsible of translating text into actionable fields, for example, extracting error codes